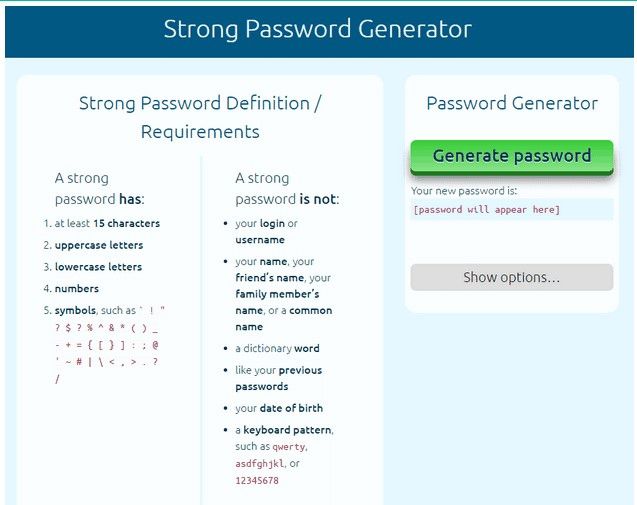
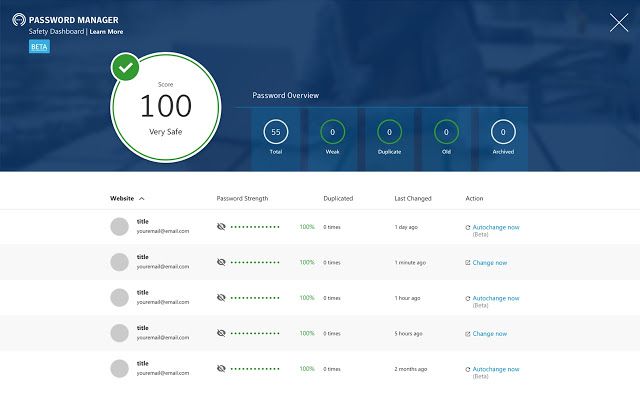
BDCC | Free Full-Text | Intelligent Security Model for Password Generation and Estimation Using Hand Gesture Features

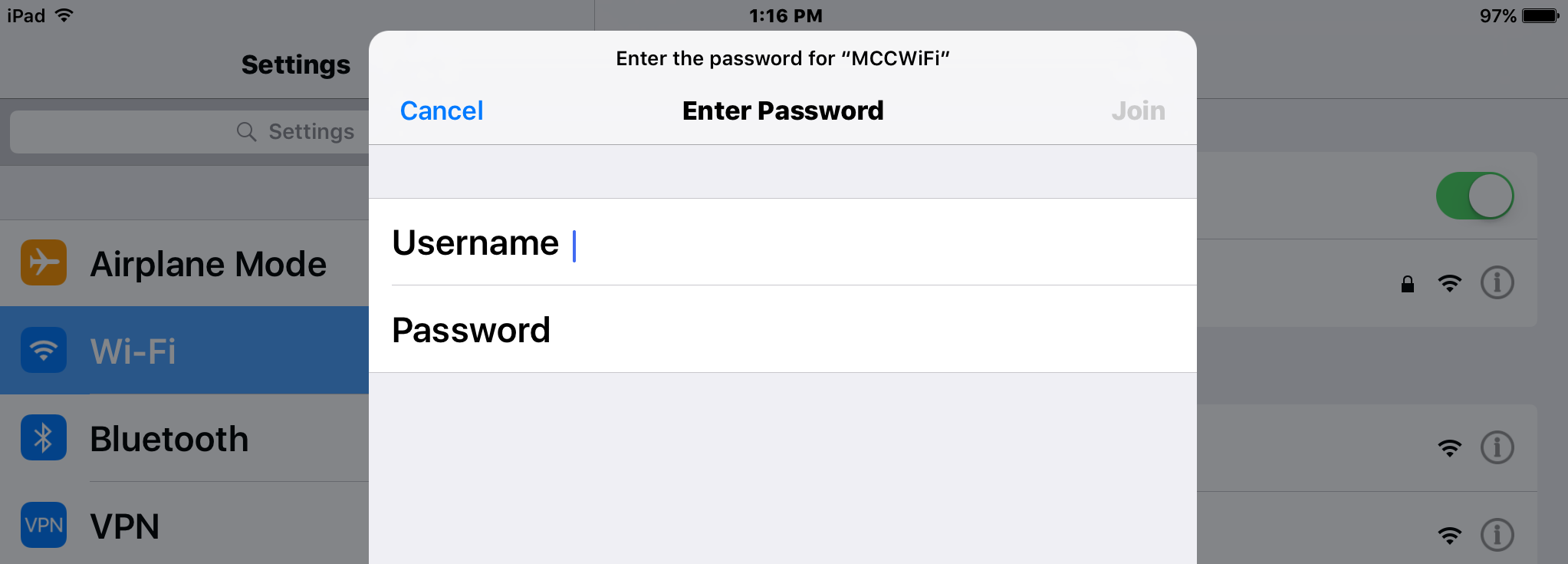
WiFiSolutions: Changing Your WiFi Password | Changing your WiFi password regularly helps make your connection more secure. Here are the steps on how to do it. Get more tips from #GlobeAtHome...
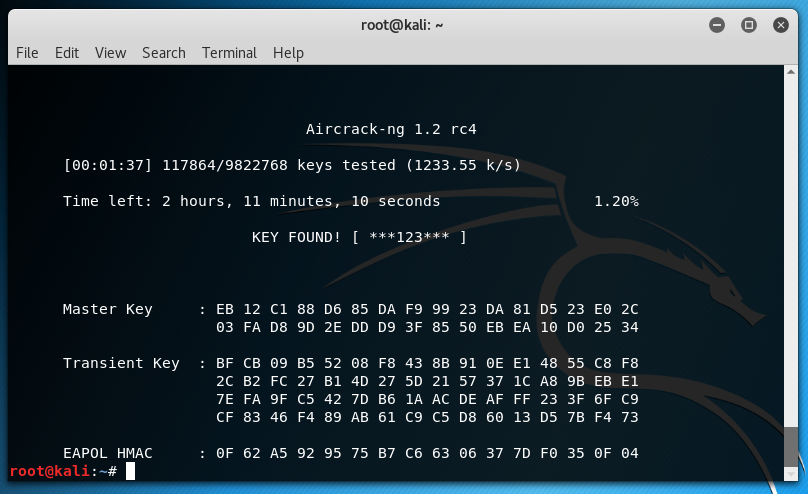
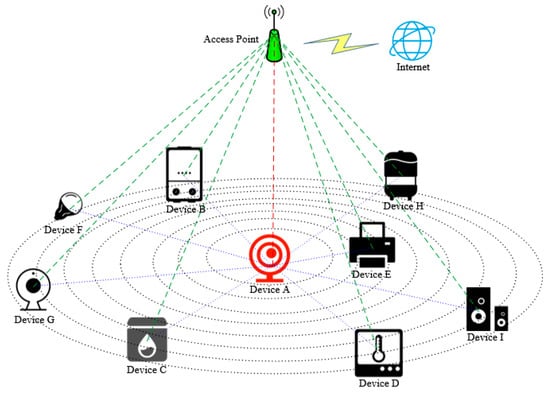
How I hacked into my neighbour's WiFi and harvested login credentials? | by Aditya Anand | InfoSec Write-ups